A Mobile Device Management Service (MDM Service) is what is used to remotely manage all aspects of mobile devices. A "mobile device" does not only mean phones and tablets. MDM service applies to all types of devices that can be remotely connected to and managed. Usually, such devices are running a modified version of the Android Operating System in order to be managed. To do this, one must have configured a mobile device management (MDM) service.
Enterprises face unique challenges when managing mobile devices and an MDM service is often the best choice for doing so. Lack of technical knowledge of how to manage devices is one challenge. But this is often solved by having a strong IT team that can deal with this.
More often, the challenge is how to manage so many devices located in so many different locations. Only by using an MDM service can companies even hope to be able to control the configuration, policies, and various other aspects of devices. An MDM service allows fleet managers to configure and manage devices completely remotely and so obviates the need for people on the ground. And MDM service can therefore also greatly reduce costs.
In this article, we're going to take a deep dive into what an MDM service is, how much an MDM service costs, what one can expect an MDM service to deliver, and exactly how to go about and implement an MDM service for the devices under your management.
What is MDM service?
An MDM service is used to provision, configure, and manage embedded devices remotely. Sometimes, this service is outsourced to a third-party provider but can also be done directly by a fleet manager, given the correct device management tools.
What software components does an MDM service consist of?
MDM service certainly uses plenty of software components to achieve its ends.
You can think of MDM service as a suite of tools and infrastructure necessary to remotely manage devices.
MDM service usually consist of the following software components:
- The operating system of the device itself must be programmed to communicate with an MDM service server, and to handle all MDM service requests that get sent to it. This must be specifically programmed into the operating system.
- The backend infrastructure of the MDM service will utilize various types of software to build new versions of operating systems to send to target devices.
- The best MDM as a service will also have some type of cloud interface software that can be accessed via a web browser to be able to manage devices.
Why is an MDM service necessary?
With the immense growth of mobile device use, many companies have adopted a mobile-first strategy. Furthermore, companies are counting more and more on mobile devices to perform business-critical functions. Many companies have invested in creating entire fleets of homegrown mobile devices to handle everything from point of sale functions to ticket reading systems. Kiosk systems have also become popular.
Even in the smallest businesses, the number of mobile devices can be huge.
Maintaining so many devices can be a logistical nightmare, and that's not even to mention ensuring that they remain secure. Many such devices have access to highly sensitive business information. An MDM service allows fleet managers to maintain device security remotely, and to be alerted whenever any device security policies have been violated.
Typically, an MDM service is outsourced to an external company that has built the necessary infrastructure to offer a turnkey MDM service solution. That's because building an MDM service that functions properly requires tremendous resources and knowledge across multiple stacks of technology.
What is covered in MDM services?
The service MDM offers is to manage every single aspect of a device's configuration, security policies, apps, settings, and so on.

An MDM service can be applied to any type of device that has been properly configured for it so long as the infrastructure for that MDM service is in place.
Such an infrastructure is a fairly enormous task to implement because remotely managing devices with an MDM service isn't only a matter of the device having the proper operating system running on it, but also of the robustness of the backend support to provide MDM services to the device.
An MDM service typically needs to take care of:
- Hardware needs (such as firmware updates)
- Software (operating system updates and app updates)
- Security (applying company policies to devices, detecting when they are not implemented)
- Encryption
- Authentication (ensuring only authenticated devices can communicate with MDM service)
- Configuration
- Basic device settings
Let's look at some of these aspects in detail:
MDM service for hardware
The correct hardware is required for an MDM service to function properly. This applies to both the device itself and also to the backend infrastructure.
On a device level, the hardware needs to support an operating system that can connect to an MDM service. Not all operating systems allow for this, and even stock Android doesn't come with an MDM service integrated into it. Only modified versions of Android that have had this specifically coded into them can communicate with an MDM service.
Also, the hardware needs to be powerful enough to run a fully-fledged operating system, such as Android on Raspberry Pi or on the Intel® NUC. The easiest way to do Raspberry Pi fleet management is to use an MDM service.
On the backend of an extensive MDM service, an enormous amount of server power is needed to handle code builds and operating system updates.
Software in an MDM service
Like hardware, software applies to both ends of the MDM service: The backend and on the device itself.
The backend of the MDM service must often be equipped with custom-built software to handle all aspects of the MDM service.
Ideally, an MDM service would be managed from some sort of cloud software interface. This software would be designed for administrators to manage devices directly.
But the primary area where software applies to an MDM service is at the device level. Using an MDM service, you can:
- Install/uninstall/update apps on the target device
- Trigger operating system updates (also known as over-the-air, or OTA updates)
MDM service security management
Device security management is a key aspect of an MDM service. Company device policies can be applied to the device remotely, ensuring they remain in compliance.
An MDM service allows fleet managers to enforce policies such as:
- Setting rules for device passwords so that they are strong enough to withstand brute force attacks
- Defining auto-lock settings so the device locks itself after a certain amount of time has elapsed
- Setting up device restrictions, such as limiting the use of the device's camera. This might be necessary for confidential locations. Other restrictions can also be placed, such as limiting the use of certain types of apps, preventing the download of certain types of content, blocking Bluetooth, and so on.
- Enabling or disabling system extensions that could pose a security risk
- Enabling geofencing so that certain features/apps of the device only function within a certain geospatial radius.
An MDM service is crucial for enterprise device management, from a security perspective. Because enterprise devices often have access to critical business data, it is imperative that fleet managers can control every detail of these devices' security from a distance.
An MDM service also allows fleet managers to set up rules for wiping devices, or to manually wipe devices if they have been compromised.
Over-the-Air updates
One of the most important aspects of an MDM service is the ability to carry out "Over-the-Air software updates," also known as OTA Updates.
OTA updates are automatic or manual updates of the device's firmware or software. The device downloads the update and then installs it.
There are different types of OTA updates. Some are incremental, and others replace the entire operating system on the device. An MDM service should be able to handle all types of updates. And the target devices and backend infrastructure must be designed to be able to handle rollbacks of updates should any particular update fail.
The entire system is quite sophisticated, but from an MDM service perspective, all a fleet manager needs to know is that these OTA updates can be triggered:
- Manually
- Automatically
Once a fleet manager has configured a mobile device to connect to the MDM service, OTA updates can be done automatically on a schedule, or the OTA updates can be sent manually to a device by a fleet manager. All of this is fully within the control of the fleet manager using an MDM service.
Using an MDM service, you can also send OTA updates to just a single device as a test, to a subset of devices, or to the entire fleet. This way, you can ensure maximum uptime in the rare case that one of the updates is faulty.
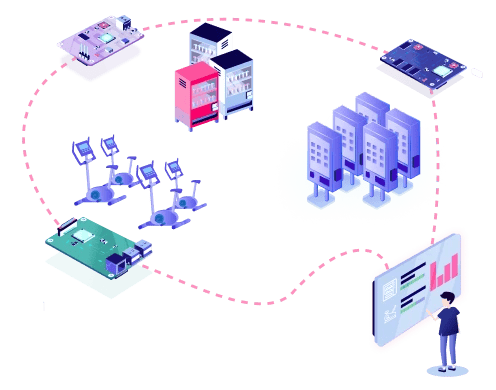
Fleet management
A properly configured MDM service provides fleet managers with full control of their fleets, whether the fleet consists of just one device, or a hundred thousand.
Using an MDM service is the only logical way to manage devices. Trying to manage them individually would be a nightmare.
An MDM service allows fleet managers to provision devices, configure them, control their software, apply company policies to them, secure them, wipe them, and handle anything on the device as if they were physically accessing it.
Fleet managers can also use an MDM service to track devices, maintain an inventory, or send alerts to devices letting their users know to take some type of action on the device.
Configuring groups of devices
Using an MDM service, you can set up devices within groups and then apply settings, software, and security policies to those groups.
For example, you could put devices in groups based on:
- Location
- Branch
- Function (such as salespeople versus consultants)
Different policies and features can be enabled or disabled according to these groups in the MDM service. For example, devices in Europe are more likely to require more stringent data protection policies compared to those in the USA. And devices in California would need different data protection policies than in any of the other US states.
Salespeople would likely need access to sales enablement software, whereas other groups might not need this. MDM for retail is essential to ensure that employees and branches have properly configured devices. Another sector where MDM is essential is MDM manufacturing.
Data collection and device monitoring
An MDM service can collect data on devices and monitor their performance, ensuring that they are functioning properly and that they are fully compliant. Should any device be found to be lacking, the fleet manager can trigger actions on the device using the MDM service.
What Is an MDM Service Provider and How Do You Choose the Right One?
Building an MDM service from scratch is a gargantuan task. It requires deep knowledge and understanding of:
- The operating system your devices use
- Backend server administrative knowledge
- Code-building and source code control
- A wide range of security topics
- And many, many other areas
An MDM service must also be constantly monitored and maintained. Like any suite of tools, new technology means that upgrades will be inevitable.
The investment for a home-grown MDM service would easily sum to hundreds of thousands of dollars, if not more. That's not to mention the huge amount of man-hours that would be required to maintain such a service.
The costs of it mean that most companies either skip it altogether, or do the smart thing and hire MDM service providers whose mainline business is to provide robust and efficient MDM services to clients of all sizes. Such a service is called MDM Managed Service because the MDM service tools are fully managed by the MDM service vendors.
Several factors come into play when choosing a company that offers MDM managed services.
1. Company reputation
The first of these is the company's overall reputation. A properly functioning MDM service requires immense investment and so one should be cautious of companies that have not proven themselves in the field. This does not mean that new companies should be avoided. It means that you should understand that industry insight and experience is crucial.
2. The management team
It's also important to look at the credentials of the company's management. The knowledge required for building an MDM service is not something you can gather from a few online courses and then two years of experience as a junior developer. An MDM service requires an in-depth understanding of high-level technology concepts, multiple programming languages, economies of scale, and other business-related factors.
The company's management team should be well educated and highly experienced.
3. The types of products the company works with
Once the above core fundamentals have been established, you should then look at the type of products the MDM service company typically works with. A company that focuses on an MDM service for personal devices wouldn't likely be a match for a company that needs to manage a hundred thousand Point of Sale devices that never leave the premises.
There are hundreds of different types of devices that can be managed through an MDM service. Try and see if the MDM service company has experience with the type of device that you need managed.
4. The service offering
Finally, you should look at what precise services the company offers. Do they provide OTA updates for devices? How is their customer support? How easy is their MDM service to use?
An MDM service might come with tons of bells and whistles but if it isn't user-friendly, it won't be any good for everyday users.
What are the monthly costs for an Android MDM service?
A combined study by Oxford Economics and Samsung found that companies typically spend between $3.25 and $9 per device registered with an MDM service. This varies according to the features that are enabled in that service.
Should you build or buy an Android MDM service?
Completely aside from the initial costs of building an MDM solution, there are also the maintenance costs to keep it secure and functioning properly. These can be huge. Finally, there is the strong possibility of technical debt — those unforeseen costs associated with doing something incorrectly because of choosing an "easy route."
MDM for small businesses is as necessary as MDM for large businesses. The benefits of MDM for businesses of any size cannot be overstated.
Building your own MDM Service is certainly not the "easy route," considering that the costs of hiring an external MDM service provider are minimal in comparison.
Emteria offers a fully-fledged MDM service for any size of fleet
Emteria has built a custom version of Android — emteria.OS — that has an MDM Service Android Function enabled out of the box. The solution offering includes the necessary backend infrastructure and resources to ensure that the MDM service stays maintained and functioning properly.
Emteria's Device Hub is a complete MDM service tool that is accessed easily from any browser. It lets you manage any devices on your fleet that have been properly registered with the Device Hub.
Emteria.OS can be installed on a wide configuration of supported hardware platforms, allowing companies to quickly build fleets of devices without having to worry about finding a compatible version of Android that can run on them.
Getting started with emteria.OS and its associated Device Hub is as simple as downloading the free version of emteria.OS (3 devices are free forever) required for your chosen hardware platform and then installing it. For a package fee starting at 100 devices, you benefit from free upgrades and security updates maintained by a highly experienced team of experts.
Learn more about emteria's MDM service for your fleet of devices. ⬇️
Build unique Android products, manage them remotely
See why emteria is the chosen Android™ customization & management platform for product builders — build Android products based on your requirements with all enterprise features you need.


-1.png?width=338&height=292&name=Group%202256(1)-1.png)