Android SSH allows you to access your Android device remotely and securely. This is essential in an enterprise context, where Android devices are used for all manner of Internet of Things (IoT) functions and devices.
Android SSH lets you execute shell commands against the device and transfer files securely without any size limit. If you have root access to the device, you can basically do anything on the device through Android SSH.
Let's look at Android SSH, the difference between an Android SSH client and server, and the easiest way to enable Android SSH on your devices.
What is SSH?
SSH stands for Secure Shell or Secure Socket Shell. It's an open network protocol allowing secure communication between two devices, and it was developed as an alternative to Telnet which provided similar functionality but insecurely.
SSH uses public key encryption to encrypt all traffic between the client and the server. This is the same type of encryption that SSL uses to encrypt traffic on the internet. In public key cryptography, one of the keys is public, and the other is private.
The use of public/private keys is called asymmetric encryption because the data cannot be mutually understood by both parties. Only the party with the private key can decrypt messages encrypted with the public key.
SSH therefore only uses the public/private key encryption for the initial handshake to authenticate the client and server. By using a key exchange algorithm, the client and server create a mutually shared secret which then lets them share information symmetrically. Once that second key exists, they no longer need the public and private keys used for the initial handshake.
With the rise of mobile devices in an industrial context, the need for Android SSH has grown. Although you can somewhat control devices using Mobile Device Management (MDM) features, complete control of the device's internals is typically unavailable in MDM tools.
What is SSH used for?
SSH is used for tasks that require complete security, such as the administration of servers remotely. Once the initial handshake has been completed, any traffic passing through the SSH connection is entirely encrypted. This allows users to transfer text and files securely.
SSH can also create "tunnels" that allow other application protocols to operate securely, such as file transmission protocols, messaging protocols, remote connection protocols, and database protocols.
For example, you can connect remotely to a MySQL Server through an SSH tunnel and so prevent eavesdropping on sensitive information.
Secure Shell capabilities and security issues
SSH enables several inherent privilege elevations, such as the ability to execute sudo commands, so maintaining private keys is crucial. Once a hacker gains access via SSH, they've pretty much been given the keys to the castle.
All the basic security practices for key management come into play, such as:
- Regular key rotation policies
- Secure storage
- And privileges granted only to a limited number of users and roles to manage SSH keys.
Attackers often engage in "lateral movement" when granted SSH access due to the trusted nature of SSH connections. Lateral movement is when an attacker tries to gain access to other privileged systems.
One area that can be hardened immediately is the SSH Server's configuration. SSH providers such as OpenSSH have a huge number of configuration options, some less secure than others.
Some of the OpenSSH configuration options to toggle for better security include:
- Switching off forwarding for the X Windows system (X11) because of its inherently insecure nature
- Disable empty passwords
- Limit the maximum number of login attempts to something reasonable, such as 3 or 5
- Disable password authentication and allow only key authentication
- Disable root logins
OpenSSH
OpenSSH is one of the most popular toolsets for enabling SSH connections. It is a suite of software that implements the SSH protocol, and it's completely open-source. The software suite is already integrated into several OSes, such as Windows, macOS, and many Linux distributions.
Can you connect via SSH to Android?
Yes, you can use SSH to connect to an Android device remotely. You can do this either by installing an existing Android SSH app that turns the device into an SSH Server or by installing a custom version of Android that comes with Android SSH functionality built into it.
SSH or Mobile Device Management (MDM)?
One limitation of SSH is that an SSH client can only connect to an SSH server if it can "see" the SSH server—in other words, they must be on the same network.
Usually, when enabling an SSH server on an Android device, the device is behind a NAT—Network Address Translation, where local IP addresses get translated to a single, public IP address used to access the internet. The Android device itself isn't directly connected to the internet.
If the SSH client isn't on the same network as the server, you would either have to use a VPN or somehow expose the server. Because of this limitation, SSH is usually only used when both devices are on the same network. That's where alternative solutions such as MDM can come into play.
Android SSH use cases
What can you do with Android SSH? The use cases for Android SSH are more prominent in an industrial and enterprise context than in a personal context, such as for the remote update of IoT devices or OTA firmware updates.
Android Debug Bridge (ADB) is another way of accessing Android devices remotely. ADB's purpose is primarily to debug Android devices and apps, but it also provides a shell for transferring files and executing commands. Unfortunately, ADB isn't secure to use on devices in production.
Some of the things you can do with production devices using Android SSH include:
- Controlling devices without a connected display (known as headless devices).
- Applying updates.
- Installing apps.
- Copying and deleting data.
- Changing config files.
- Remotely administer the device.
- SSH file transfer Android.
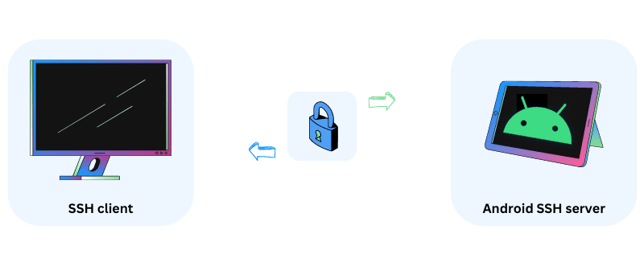
Understanding the client/server model
An SSH connection consists of a client and a server. The server executes commands that it receives from the client.
An SSH server constantly listens for connections, usually on port 22, from external clients. When it first receives a connection request, the client and server undergo the initial handshake.
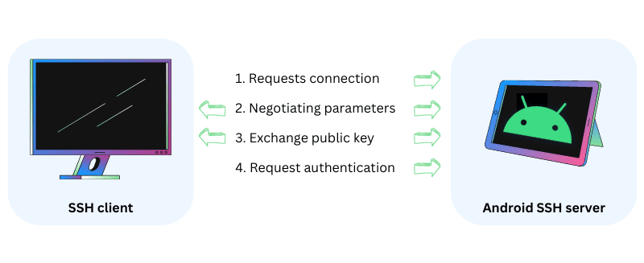
The client sends a message to the server to negotiate the connection parameters. First, telling it what SSH version it's using, and what software. So, for a client using SSH version 2, connecting via PuTTY, the string might look something like this: SSH 2.0 PuTTY_Release_0.72.
The server responds with the version and software as well. For example, SSH 2.0 OpenSSH_7.1p2 Debian-1.
After this, the client sends over what's called a KEXINIT message, which lists the encryption algorithms it supports, and the server does the same. If they cannot agree on an algorithm, the connection fails.
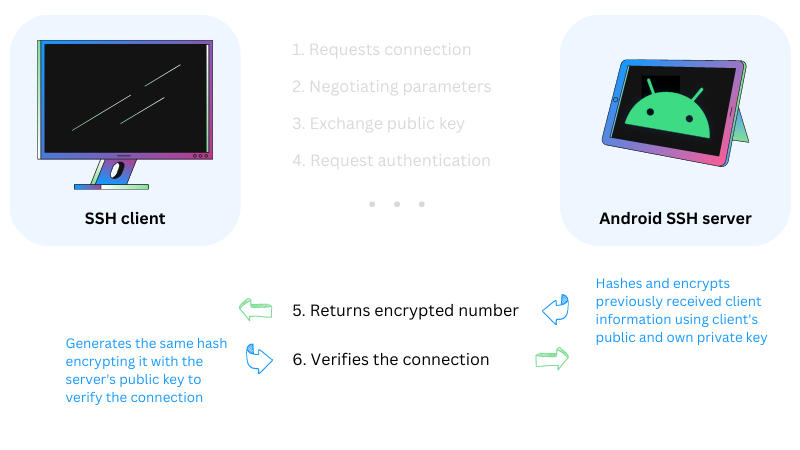
Once the server and client agree on an algorithm, such as AES256, the server needs to authenticate itself to the client. It does this by hashing several values and payloads previously sent by the client, and then encrypting that hash with its own private key. The client can generate the same hash, encrypt it using the server's public key, and so verify that it is indeed talking with the server it intended to communicate with.
This hash will be sent along with every communication to uniquely identify the session.
To SSH from Android to another server, your Android device would need an Android SSH client app. Windows users have used PuTTY for years as their SSH client. It's an excellent SSH client but doesn't provide SSH on Android or any other operating system except Windows. You would specifically need an Android SSH client to connect to an SSH server.
What is an Android SSH server?
An Android SSH server is an Android device that has SSH functionality running on it that can accept external communications from an SSH client
To SSH into Android, you need to set up an Android SSH Server. Far fewer Android SSH tools exist that enable the server side of Android SSH.
Setting up an Android SSH Server means that you can connect to your Android device using SSH from any other device. If you're connecting to Android SSH from a Windows client, you can use PuTTY from your Windows machine.
SSH Android apps—what is the best SSH client for Android?
On the client side, Android SSH is simple to configure. You don't need special permissions; plenty of apps exist that let you connect to an SSH Server from an SSH App Android. It doesn't matter if you want to use SSH from Android to Linux, or from Android SSH to Windows, you can use the same SSH Client App for Android to do it.
Some of the best-rated SSH for Android Client apps are:
- JuiceSSH
- Termius
- Terminus
- Terminux
- ConnectBot
- Admin Hand
- DaRemote
- Far Commander
Installing these Android SSH clients is relatively easy. Simply download the tool and install it and then type in the details of your SSH Server.
Unfortunately, these apps do not enable SSH for Android as an SSH server. They might be useful for IT teams accessing Windows or Linux servers from their mobile devices, but not the other way round. There are some apps that will do this but they are limited because they don't have root access.
Let's look at how to turn devices in Android SSH Servers.
How to enable SSH on Android?
You can enable Android SSH by installing an app that provides SSH server functionality or using an SSH server native to a custom Android version. Be aware that Android SSH apps will be restricted on non-rooted devices and can be forcibly snoozed by the battery optimizer.
Android battery optimizer
Android contains two major power-saving features called Doze and App Standby. The features aggressively restrict apps' access to power-intensive functions when the device is not plugged in, or an app is running in the background. One of the functions these features restrict is network traffic.
Users must go through a complex procedure of changing battery-saving settings to ensure an Android SSH server app is not caught by Android's power-saving features.
Using built-in Android SSH features instead of an app is the only way to confidently get around this limitation.
Lack of root access
The lack of root access to a device renders any perceived SSH advantages somewhat pointless. Yes, users would be able to send files securely through the SSH tunnel, but there are other easier ways to do this if that's the only feature you need from SSH.
Users wouldn't be able to run any update commands for the OS itself without root access, and would only be able to update apps.
Emteria.OS's in-built Android SSH server with root access
Emteria.OS—an Android OS for industrial applications and embedded systems built with enterprises in mind—includes rooted Android SSH server functionality out of the box. This functionality can be used to manage and control devices if their in-built MDM features ever go down or reach their limitations.
Emteria.OS also includes an MDM as part of its Device Hub, which is a browser-based hub for fleet managers to manage their Android devices remotely.
You don't need to install any special Android SSH app to use emteria's Android SSH, but you do need to configure it, just like you would for any other SSH Server.
There are four simple steps involved in enabling Android SSH through emteria:
- Enable ADB on the device.
- Set up key-based authentication.
- Disable ADB when you're finished.
- Enable connections through SSH
ADB poses some security risks for devices in production, so it's important to disable it once you've finished configuring the Android SSH server.
Emteria's Android SSH server offers the following significant advantages over other solutions:
- Native implementation based on OpenSSH—no additional apps required.
- Root access.
- Key-based authentication, which is considered the most secure way of authenticating when using SSH.
- Supports SCP (Secure Copy Protocol) for copying files securely.
- SFTP (SSH File Transfer Protocol) for securely transferring data.
You can find full details on how to enable emteria's in-built Android SSH feature in our comprehensive help article titled How to configure and enable the integrated SSH server.
Choose emteria for your enterprise Android use cases
Emteria is an Android OS which is easily customized and explicitly designed for enterprise and industrial use cases.
The beauty of open-source Android is that anybody can modify it. But enterprises need enterprise-level support and confidence that their custom Android version will receive FOTA updates and be actively maintained.
Emteria brings this to the table with emteria.OS.
Build unique Android products, manage them remotely
See why emteria is the chosen Android™ customization & management platform for product builders — build Android products based on your requirements with all enterprise features you need.


.png?width=799&height=449&name=FCM%20Alternatives(2).png)